How to Protect Crypto from Hacks in the USA: The Ultimate Guide 

Cryptocurrency has revolutionized how we think about money, investments, and digital ownership — but with innovation comes risk. For people in the USA, ensuring the safety of crypto assets is critical due to a rising number of cyberattacks, exchange breaches, and phishing schemes.
In this comprehensive guide, you’ll learn how to protect your crypto from hacks, best practices, tools you should use, comparisons between security options, and links to official sources like the Federal Bureau of Investigation (FBI), Cybersecurity & Infrastructure Security Agency (CISA), and leading wallet providers.
Why Crypto Security Matters in the USA
Cryptocurrency isn’t “stored” in banks like traditional money. Instead, ownership is controlled by private keys — powerful digital credentials that unlock access to your crypto holdings. If someone steals your private key, they essentially steal your crypto.
According to the FBI’s Internet Crime Complaint Center (IC3), cryptocurrency theft and fraud have been major targets of cybercriminals, with losses in the hundreds of millions annually. Staying informed and proactive is your best defense.
📌 FBI IC3 Official Site: https://www.fbi.gov/ic3
Common Crypto Threats Every Investor Should Know
To defend your assets effectively, it’s important to understand how hackers typically operate:
Phishing attacks — fake emails or websites that trick you into revealing login credentials.
Exchange breaches — even big platforms can be hacked if security is weak.
Malware & keyloggers — software that records your keystrokes or steals keys.
SIM swapping — attackers hijack your phone number to bypass authentication.
Ransomware — malware that holds your devices ransom until you pay with crypto.
For more on emerging threats and national advisories:
🌐 CISA Cybersecurity Alerts: https://www.cisa.gov/uscert/ncas
Top Strategies to Protect Your Crypto
Below are actionable steps every USA crypto investor should implement:
🔐 1. Use a Secure Wallet (Cold Wallet Recommended)
Crypto wallets fall into two main types:
Hot Wallets — connected to the internet (e.g., software wallets, exchange wallets).
Cold Wallets — offline storage devices (hardware wallets like Ledger or Trezor).
Cold wallets are widely considered the safest because they are offline, making them far less accessible to hackers.
| Feature | Hot Wallet | Cold Wallet |
|---|---|---|
| Internet Connection | ✅ Yes | ❌ No |
| Easy Access | ✅ Yes | ⚠️ Moderate |
| Best for Large Holdings | ❌ No | ✅ Yes |
| Protection from Hacks | ⚠️ Moderate | ✅ Excellent |
👉 Which Is Right for You?
Frequent trader? A hot wallet might be easier for daily use.
Long-term holder / large amounts? A cold wallet is strongly recommended.
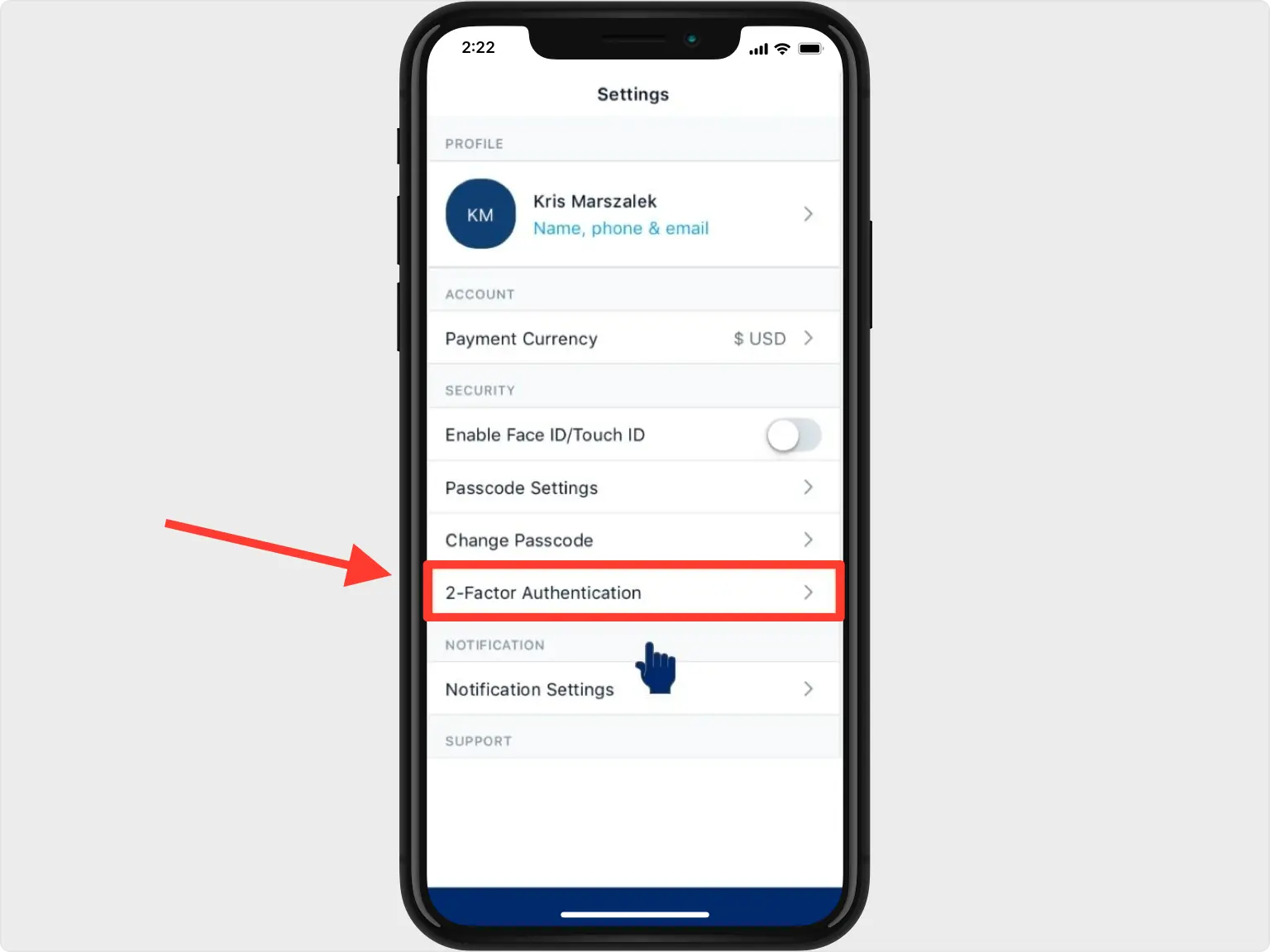
📲 2. Enable Two-Factor Authentication (2FA)
Two-Factor Authentication adds an extra layer of security beyond your password. Avoid SMS-based 2FA if possible and use authenticator apps like:
Google Authenticator
Authy
Duo Mobile
These are far safer against SIM swaps and phone porting attacks.
📛 3. Never Share Your Seed Phrase or Private Keys
Your seed phrase is the master key to your wallet. No legitimate service will ever ask for it.
Never take screenshots of your seed phrase.
Never save it digitally.
Store it in a secure physical location or a fireproof safe.
🛡️ 4. Use Reputable Exchanges Only
Not all exchanges are built equally. In the USA, prioritizing regulated platforms with strong security measures is critical:
Coinbase – insured custodial protection for stored assets.
Kraken – advanced security features and global presence.
Gemini – regulated exchange with insurance coverage.
Always verify that the exchange you choose complies with U.S. regulations.
🧾 5. Practice Good Digital Hygiene
Small habits can protect you from large losses:
Use strong, unique passwords (password manager recommended).
Keep software updated (wallets, devices, operating systems).
Beware of phishing attempts — always check URLs carefully.
Avoid clicking suspicious links on social media.
Comparison Table: Crypto Security Tools & Methods
| Security Tool / Method | Ease of Use | Protection Level | Cost |
|---|---|---|---|
| Ledger (Hardware Wallet) | Moderate | ⭐⭐⭐⭐ | $$ |
| Trezor (Hardware Wallet) | Moderate | ⭐⭐⭐⭐ | $$ |
| Authenticator Apps (2FA) | Easy | ⭐⭐⭐ | Free |
| Multi-Signature Wallets | Advanced | ⭐⭐⭐⭐ | Variable |
| Exchange Wallet Only | Easiest | ⭐⭐ | Free |
Risk Disclaimer
Cryptocurrency investments carry inherent risk, and past security performance does not guarantee future protection. While the measures outlined in this guide aim to reduce the likelihood of hacks and thefts, no system is 100% immune. Always do your own research and consider consulting with a qualified financial or cybersecurity professional before making investment decisions.
✅ Official and Authoritative Resources
Here are direct links to trusted organizations and resources:
Federal Bureau of Investigation (FBI) – IC3: https://www.fbi.gov/ic3
Cybersecurity & Infrastructure Security Agency (CISA): https://www.cisa.gov
Coinbase Security Info: https://www.coinbase.com/security
Ledger Official Site: https://www.ledger.com
Trezor Official Site: https://trezor.io
🚀 Call to Action
If you’re serious about protecting your crypto holdings, take the next step:
👉 Compare investment platforms and security tools to find the best fit for your crypto strategy.
👉 Check current rates and fees before choosing a wallet or exchange.
About the Author
Azka – Financial Enthusiast
Azka is a passionate financial enthusiast focused on empowering individuals to invest wisely, stay secure, and navigate digital assets with confidence. With expertise in investment strategy, digital finance, and cybersecurity best practices, Azka helps readers make informed decisions in the modern financial landscape.

